Gonçalo Magalhães
Head of Security at Immunefi
A proteger milhares de milhões na economia on-chain.
A construir agentes de segurança com IA.
Blog
Experiência


Palestras & Media
Speaking Engagements
DEFCON's Bug Bounty Village
Porque deves caçar bugs em Bug Bounties Web3
Apresentação sobre as distinções chave da caça de bugs Web3 e como a blockchain oferece mais garantias aos whitehats. Cobriu hacks significativos, comunicações com hackers e bounties milionários.
ETHDam 2024
Auditores e Caçadores de Bounties: quem deve proteger os teus fundos?
Discussão em painel com Oliver Hörr (hats.finance), Erik Arfvidson (Euler Labs) e Josselin Feist (Trail of Bits), moderado por Matthias Egli (ChainSecurity).

TrustX 2023 (DevConnect Istanbul)
A Mentalidade Hacker: O que leva ao sucesso no mundo dos Bug Bounties
Palestra a explorar a mentalidade e estratégias que levam ao sucesso na caça de bugs, apresentada na TrustX durante a DevConnect Istanbul.

Solidity Summit 2023 (Devconnect)
As armadilhas de segurança mais comuns em Solidity (e as melhores proteções)
Palestra sobre as vulnerabilidades de segurança mais comuns em smart contracts Solidity e as melhores práticas para as prevenir.
Media Mentions
Featured Quote on Back Cover
"I've taught crypto devs for many years. If you want to go from zero to hero in smart contracts, Mastering Ethereum is the definitive no-fluff guide I recommend above all to achieve that."

Hacking Back: Why Offensive Cyber Operations Are a Legal Minefield
"This is why firms should focus on operating under frameworks that prevent these scenarios entirely, like scaling bug bounty programs that channel security efforts into authorized, constructive activities. When security researchers work within this framework, they're protected legally, companies get stronger security, and innocent third parties are never put at risk."

Lazarus Group's favorite exploit revealed — Crypto hacks analysis
"[North Korean hackers] focus on a small number of high-value targets and can play a very long game, combining detailed technical knowledge with social engineering and spear-phishing capabilities."
Hack Analysis: 0xbaDc0dE MEV Bot, September 2022
"In this article, we will be analyzing the exploited vulnerability in the 0xbad smart contract without looking at any actual source code. We'll analyze the massive profit arbitrage transaction and see what we can learn from there, but also try a few decompiling tools to help us reach the same conclusion as the hacker."
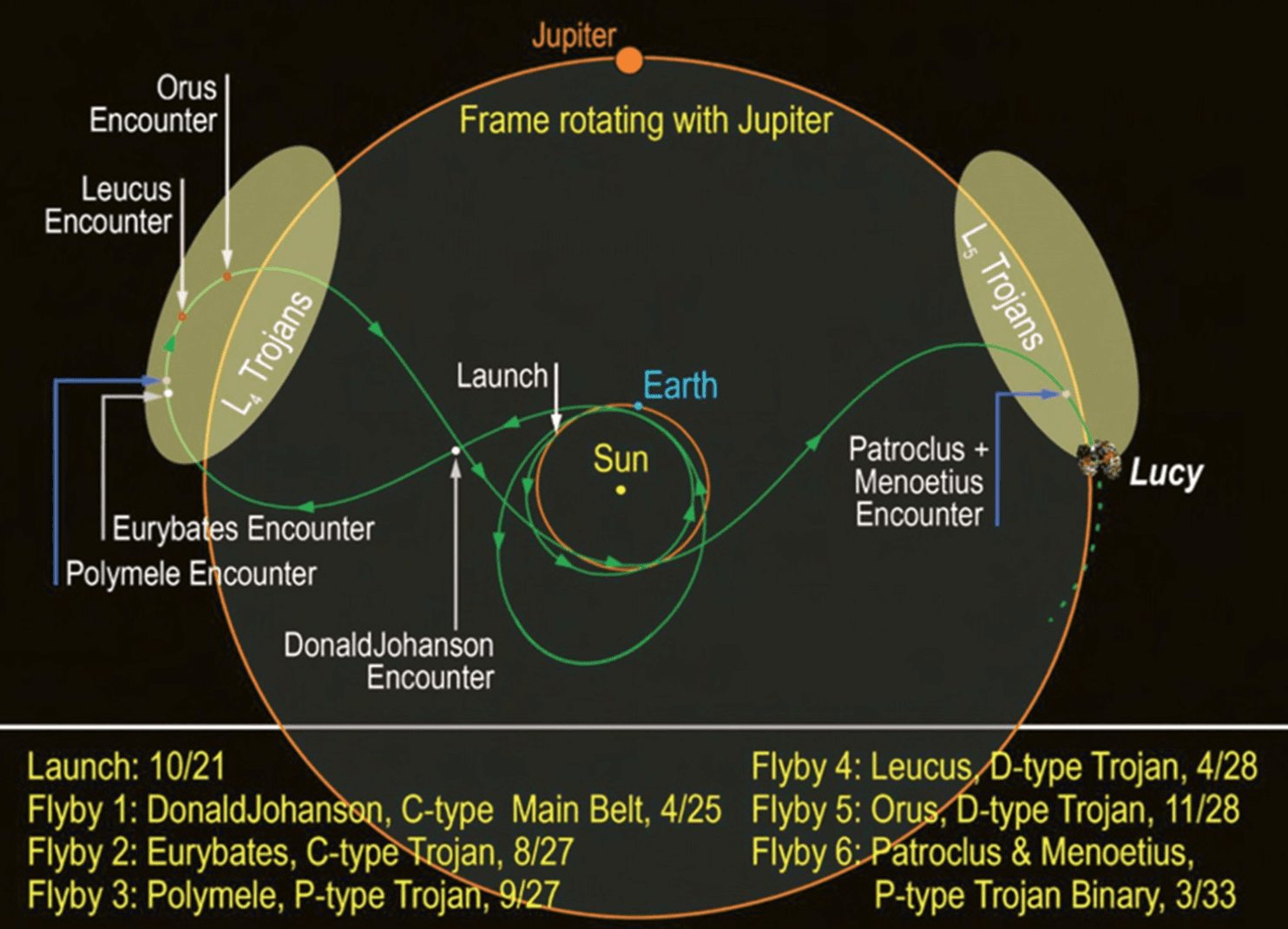
Two probes will explore the early Solar System
"The points derive from the three-body problem, which considers the gravitational pull of just two bodies (in this case, the Sun and Jupiter), and then the few points where smaller points can remain stable are found through algebraic methods. The Trojan asteroids are celestial bodies that gathered around Jupiter's L4 and L5. The Lucy mission is crucial to understanding the history of the solar system."
Contacto
Vamos Conversar
Cibersegurança, Web3, IA ou uma ideia para colaborar? Manda mensagem por qualquer um destes canais.
Tempo de resposta típico: 24-48 horas